The Digital Recoil
The Real Reason behind the NHS Code Blackout
Loading
Linux is a free Open Source computer Operating System and foundation upon which the Internet is built. Open your mind to the possibilities of Open Source software and the Open Source community.
96.3% of the top one million web servers are running Linux.
An estimated 35M desktop users, with 1.6Bn on Android phones

 05May
05May 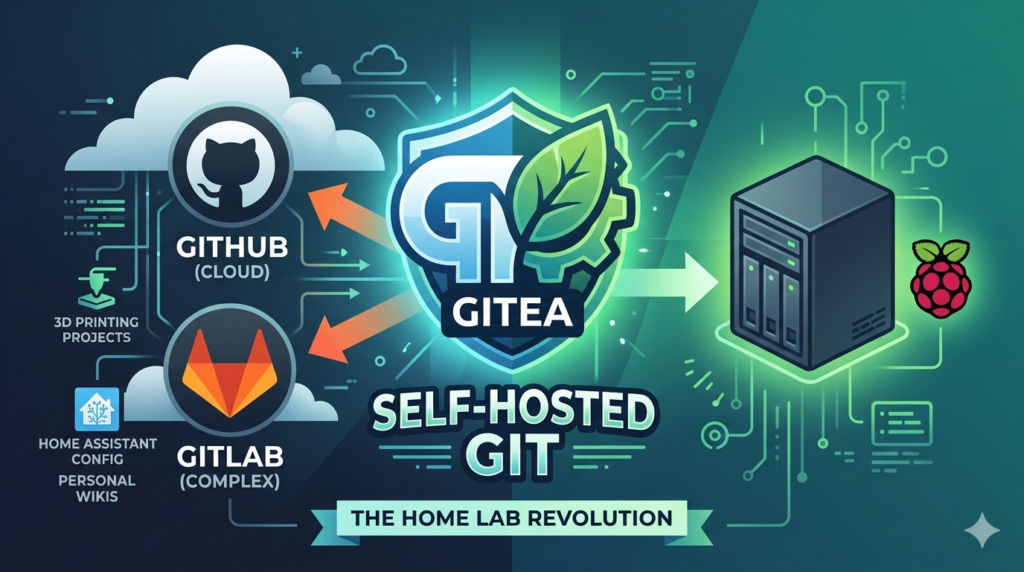 03Apr
03Apr If you're looking for on-prem Git alternatives, look no further!
 01Apr
01Apr A Bigger Issue ... So while various governments and institutions are off...
Just to be clear, LINUX is not a product, nor is it an organisation. It is a free and Open Source computer Operating System Kernel that generally comes packaged as a complete computer Operating System in the form of a "distribution". These distributions are typically also free and can be used as an Operating System on many computers in place of the system supplied with the computer. This Website is presented and managed by Linux enthusiasts with in interest in promoting the use of Linux in the UK. If you have been pointed at this website by your hardware vendor, please feel free to ask for help, but appreciate that we are not a commercial organisation with any affiliation to hardware vendors and hence not any kind of official support channel.
Linux is a powerful Operating System that performs well as a Server and on the Desktop
There are many different Linux distributions available designed to meet a range of needs
Unlike some systems, security is a fundamental design principle from the start
The source code is all there, you can literally change whatever you want
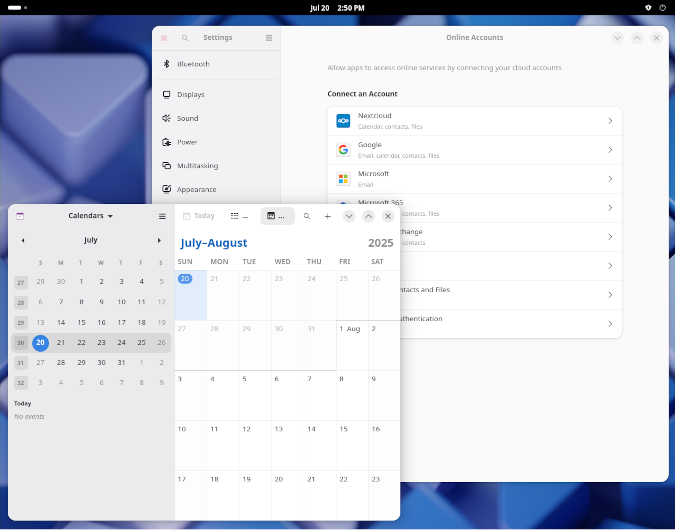
One of the leading desktops for Linux, Gnome has been around since 1999 and has evolved into a very competent and fully featured desktop that won't feel too Alien to users moving from Mac based environments. A good place to start for new users, runs on most hardware from Raspberry Pi 5's upwards.
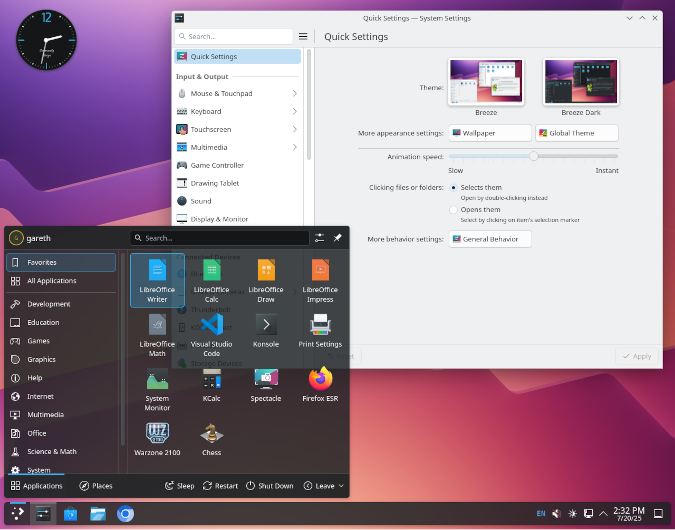
The second of the two most popular desktops, KDE evolved as a part of the Qt graphics project and probably has a more familiar feel to Windows users. Historically a less focused on graphics and more on functionality it now compares very well to Gnome in all respects. Similar resource usage to Gnome, if not a little less.
If you are currently running what might be called a commercial Operating System on your computer (as in one you had to pay for, or one you will have to pay to update) then consider that there maybe something better, and it might be free! The nay-sayers might tell you that nothing is for Free, but Linux was free when it first became available in 1991, and it's still free today!
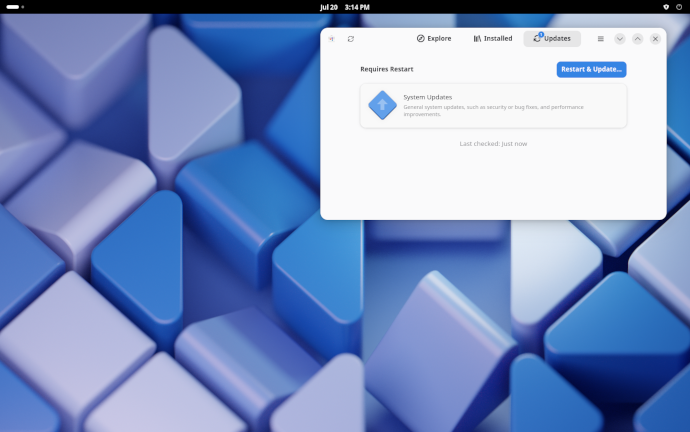
Most Linux distributions offer free updates that are available individually as they are published. This usually happens in the background, takes place quickly and doesn't stop you from working while in progress.
All distributions come with a library of packages applications which are designed to work with the distribution. The larger distributions include graphical front-end's for point and click package management.
Well, many if not most things.If it's not available via the app store then there are many more apps out there you can download directly from the vendor. If in doubt, ask on the for forms and see what other people are using.
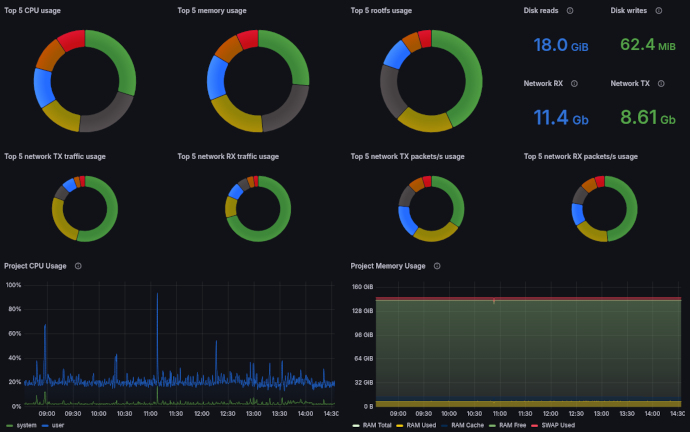
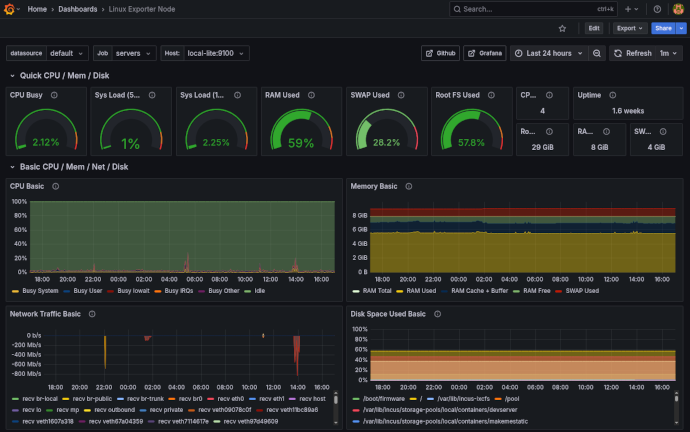
Whether you are running a domestic computer, a home server on a Raspberry Pi, an office Server on your own rack-mount servers, or as virtual machines in the Cloud, the default choice for most people is going to be Linux. The only real question is "which" Linux distribution best suits your server needs
Linux has always been security focused which is more important than ever in online environments.
If you're looking for a capability, if it's available then it's likely supported by Linux
The Origins of Linux are based on skilled programmers designing systems to solve their own problems. This is fundamentally why Linux is a free system, if you create something great for yourself rather than to make money, it's only natural to want to share it as something that will also be great for other people.

The thing with Linux is that the developers themselves are actually customers too: that has always been an important part of Linux.